Operational environment - example¶
The following figure shows the setup of the Industrial Edge system as an example.
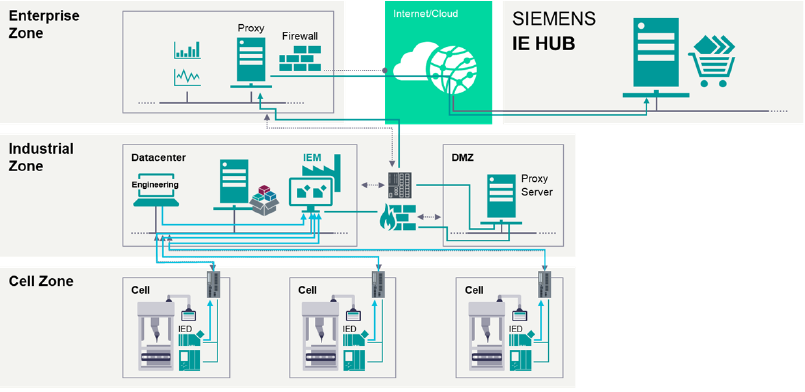
The customer IT security concept needs to decide and adjust the setup and network protection concept. The Industrial Edge Management and Edge Devices must not be operated in non-trusted networks.
In general, all system components are initializing connections from lower level to upper level using a secured communication channel.